Email shouldn’t be forgettable. We have assembled the best email signature tools that will generate a professional email signature.
What is an email signature?
An email signature is a personalized block of text that is auto generated at the bottom of every email message. A free email signature serves as a great way to create brand recognition for every message you send. Anemail signature also provides important contact details to your recipients, such as your name, job title, phone number, and email address. This allows your recipients to get in touch with you easily.
What should I include in my email signature?
- First and last name
- Company name
- Title and department
- Company physical address
- Company website URL
Other options to better personalize your email signature include:
- Business profile social links
- Business headshots
- Company logo
- Promotional opportunities or statements
- Call to action maybe for free download, demo, or trial with your company
What is an email signature generator?
Email signature generators are online tool that helps professionals build custom signatures that can then be uploaded to your current email and auto generate on each email you send. These online tools have custom templates that allow you to better personalize your email signature through inclusion of brand imagery, photos, clickable links, and more to help you better personalize your outreach and provide more memorable brand recognition.
Below are some awesome free email signature templates available online:
1. Hubspot email signature generator
Hubspot provides an email signature generator tool that allows you to browse various defined templates with different features so you can better personalize your email signature, including photos, social media links, location, and more. Just input your signature details in the fields it asks for, and you will have a custom signature available to you in minutes.

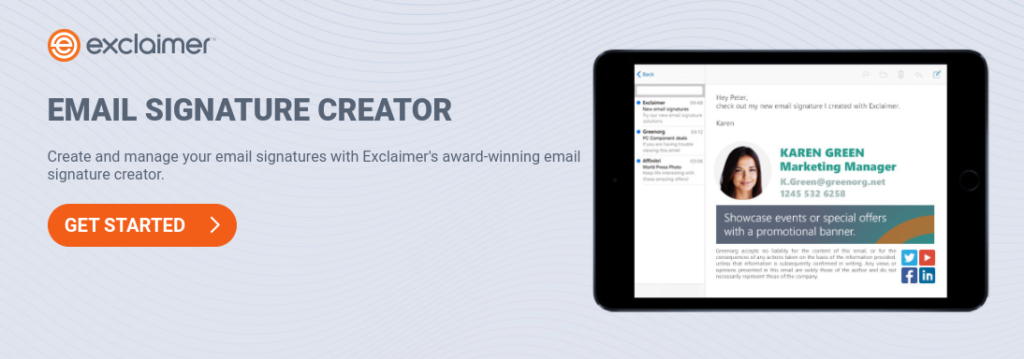
2. Exclaimer
Exclaimer is a great tool for larger organizations that need a standardized email signature format for all employees. Using the online tool, professionals can create a signature that includes features such as headshot photos, contact information, and banner ads with company promotions. Once a signature is created, its template can be shared among an organization to create a standardized email signature format for companies. This tool is also compatible with commonly used email platforms such as G Suite and Microsoft.
3. Gimmio
With a satisfaction rating of 4.8/5, Gimmio allows for endless customizability options for creating an awesome email signature. Gimmio provides customizable layout options, a number of different styling features (such as the ability to upload multiple images or banners), and shareability for larger organizations. The email signature template can also be translated easily into other business marketing materials such as business cards or employee badges.

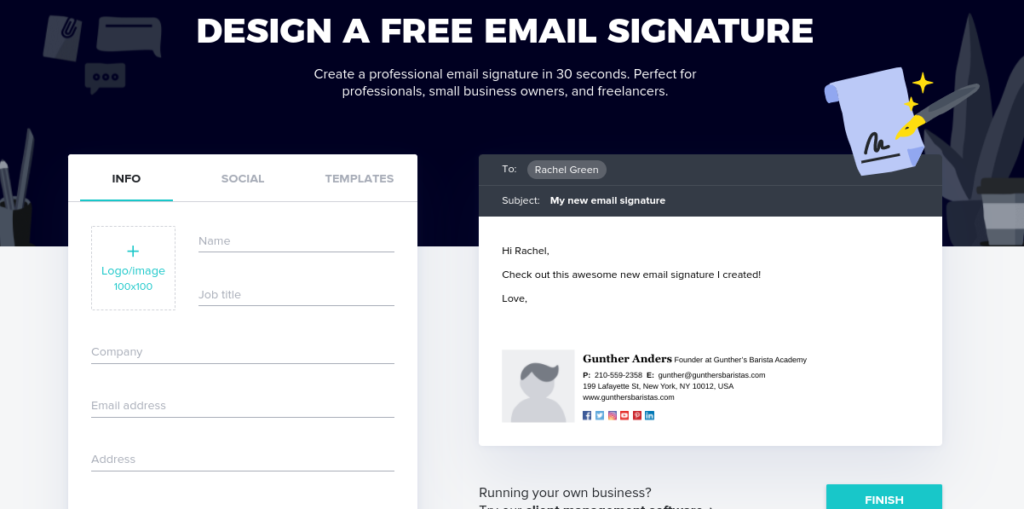
4. Designhill
Designhill allows you to create a professional brand identity through an easy to use online signature generator tool. You can create an email signature in less than one minute with auto generated fields to upload contact information and links. The tool also includes multiple templates to better customize your design, and is compatible with different social media platforms to help increase brand awareness. Once your custom design has been created, you can preview your signature on a blank email template to ensure it appears just as you want it. Designhill works on most commonly used email platforms such as Gmail, Apple Mail, and Outlook.

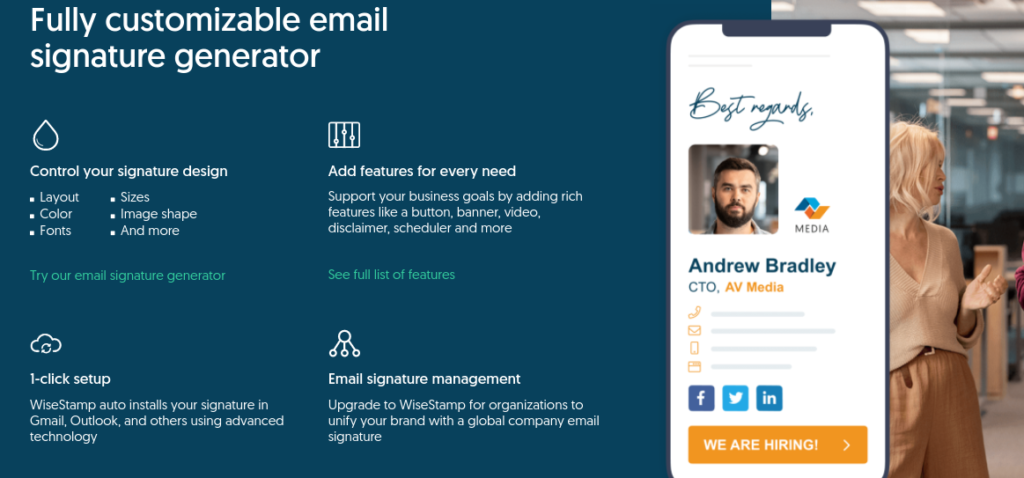
5. Wisestamp
Wisetamp allows you to create the perfect email signature whether you are a professional, freelancer, or small business owner. Wisestamp offers many different customizable features such as layout, color scheme, font choices, and sizes. Within the program you choose different tabs to alter the template, design, email provider, social media platform, and additional add ons such as banners, links, buttons, and more.
6. Mail Signatures
Mail Signatures is a great tool for professionals that need to draft up a quick signature in minutes. This tool is very user friendly, free, and easy to use. Simply choose an email platform and template, then fill in your contact details, company data, graphics, style and social media links and an email signature will be provided for your use immediately.

7. Xink
Xink allows for administrators to create a cohesive design for email signatures across their company. Once a signature is created, it can then be transferred among marketing and IT/Departments for easy setup. Xink allows you to create branded signatures that help businesses achieve measurable marketing results through the inclusion of banners to promote content and share updates and achievements. Xink will also provide analytics on which employee signatures and banners resulted in clicks and improved conversion rates. Xink is fully compatible on mobile devices and online support is available upon request.

8. Honeybook
Honeybook is another tool that allows professionals to create a unique email signature in seconds. While it does not have as many customizable features as some of the tools mentioned above, it is fairly straightforward and easy for anyone to use. All you have to do is fill in the contact fields, upload a photo or logo, add social links, and select the perfect template and you’ve got an email signature that is ready to use.
9. Signature.email
Signature.email allows organizations to establish uniformity among its employees’ email signatures to give a more professional brand image. The tool provides an easy to use drag and drop editor to upload images or company logos. Then other elements can be further customized such as fonts, color schemes, and sizes. All fields on the templates can also be rearranged, giving you complete control for the look and feel you want for your brand.

10. MySignature.IO
Mysignature.io allows professionals with non technical backgrounds to create unique email signatures from any device, even on the go. Just select your template and choose the format, organization of different elements, color, and style, and you can create a great email signature in minutes. Once created, the easy to use dashboard allows you to share your signature with other employees at your organization for a professional streamlined look.

Want to take your digital marketing strategy up a notch? Alliance Interactive is a full-service Washington, DC based digital agency and a leader in digital marketing solutions that attract new visitors and improve online conversions. We offer everything from custom website design, SEO, content creation, and email marketing, to PPC, advertising, social media marketing, and landing page design. For more information, visit www.allianceinteractive.com